Overview
RADIUS server
NPS is the Microsoft implementation of the RADIUS standard specified by the Internet Engineering Task Force (IETF) in RFCs 2865 and 2866. As a RADIUS server, NPS performs centralized connection authentication, authorization, and accounting for many types of network access, including wireless, authenticating switch, dial-up and virtual private network (VPN) remote access, and router-to-router connections.
RADIUS clients are network access servers, such as wireless access points, virtual private network (VPN) servers, 802.1X-capable switches, and dial-up servers. RADIUS proxies, which forward connection request messages to RADIUS
servers, are also RADIUS clients.
When you deploy Network Policy Server (NPS) as a Remote Authentication Dial-In User Service (RADIUS) server, NPS performs authentication, authorization, and accounting for connection requests for the local domain and for domains that trust the local domain.
This blog post shows how to Implementing RADIUS Authentication with Remote Desktop Services
Prerequisites
This section details the prerequisites necessary before integrating Azure MFA with the Remote Desktop Gateway.
Before you begin, you must have the following prerequisites in place.
- Domain Controller
- Remote Desktop Services (RDS) infrastructure
- Azure MFA infrastructure
Remote Desktop Services (RDS) and Azure MFA infrastructure
You must have a working Remote Desktop Services (RDS) infrastructure and Azure MFA infrastructure in place If you do not, then you can follow the steps Installing and Configuring Remote Desktop Services (RDS) and Implementing Azure Multi-Factor Authentication (MFA) Server On-premises with High Availability (HA)
Configure RADIUS timeout value on Remote Desktop Gateway NPS
To ensure there is time to validate users’ credentials, perform two-step verification, receive responses, and respond to RADIUS messages, it is necessary to adjust the RADIUS timeout value.
On the RD Gateway server, open Server Manager. On the menu, click Tools, and then click Network Policy Server.
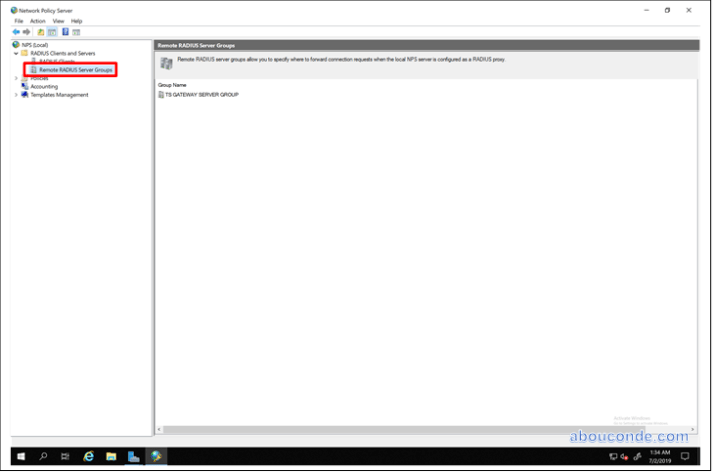
In the NPS (Local) console, expand RADIUS Clients and Servers, and select Remote RADIUS Server Groups.
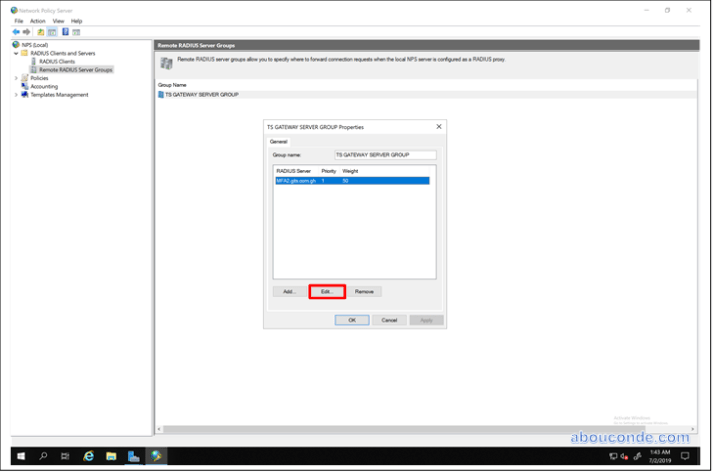
In the details pane, double-click TS GATEWAY SERVER GROUP.
In the TS GATEWAY SERVER GROUP Properties dialog box, select the IP address or name of the NPS server you configured to store RD CAPs, and then click Edit.
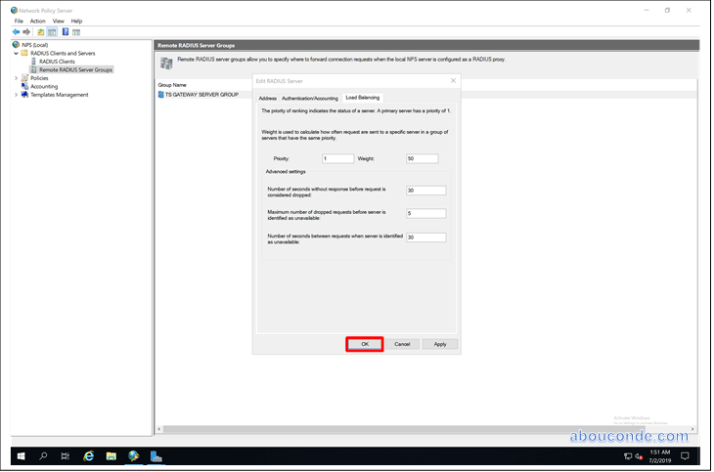
In the Edit RADIUS Server dialog box, select the Load Balancing tab.
In the Load Balancing tab, in the Number of seconds without response before request is considered dropped field, change the default value from 3 to a value between 30 and 60 seconds.
In the Number of seconds between requests when server is identified as unavailable field, change the default value of 30 seconds to a value that is equal to or greater than the value you specified in the previous step.
Click OK two times to close the dialog boxes.
Prepare NPS to receive authentications from the MFA Server
Right-click RADIUS Clients under RADIUS Clients and Servers in the left column and select New.
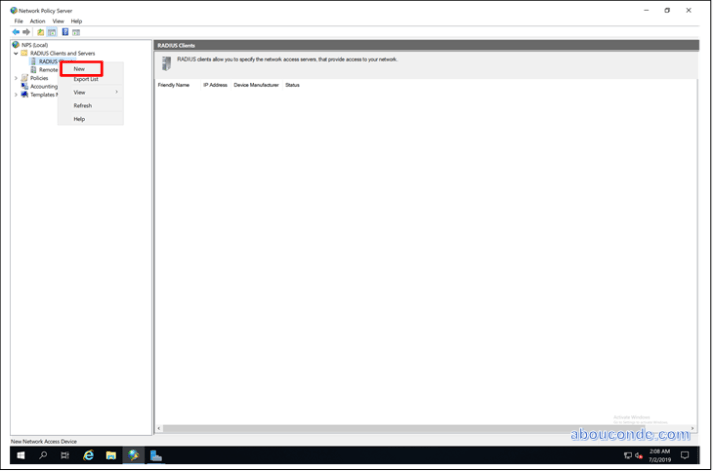
Add the Azure Multi-Factor Authentication Server as a RADIUS client. Choose a Friendly name and specify a shared secret.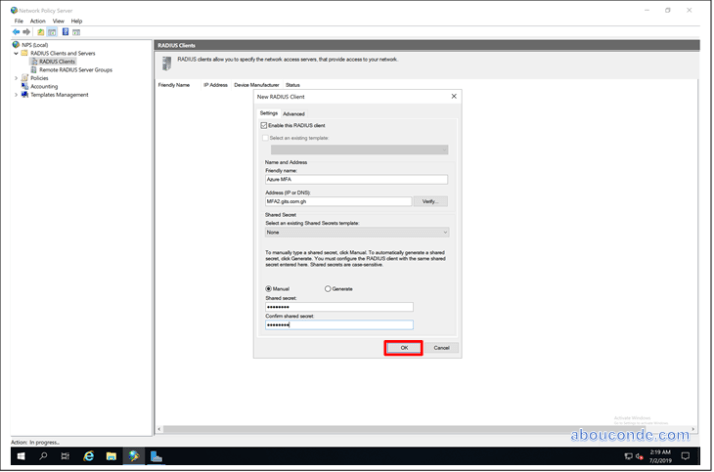
Configure Connection Request Policies
Connection request policies are sets of conditions and settings that allow network administrators to designate which Remote Authentication Dial-In User Service (RADIUS) servers perform the authentication and authorization of connection requests that the server running Network Policy Server (NPS) receives from RADIUS clients.
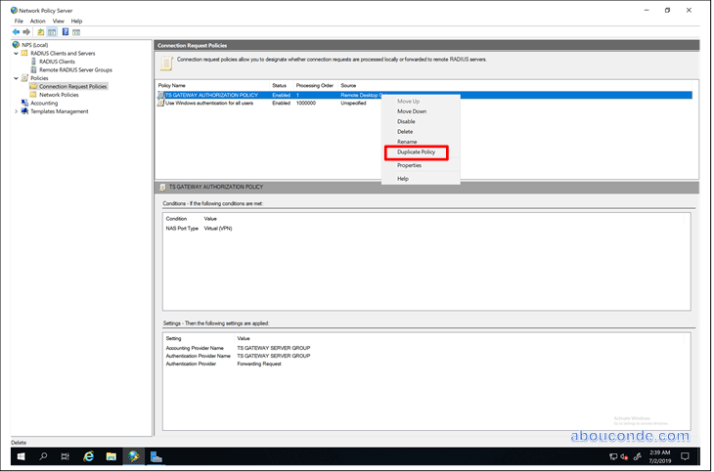
Open the Policies menu in the left column and select Connection Request Policies. You should see a policy called TS GATEWAY AUTHORIZATION POLICY that was created when RD Gateway was configured. This policy forwards RADIUS requests to the Multi-Factor Authentication Server.
Right-click TS GATEWAY AUTHORIZATION POLICY and select Duplicate Policy.
Right-click Copy of TS GATEWAY AUTHORIZATION POLICY, and click Properties.
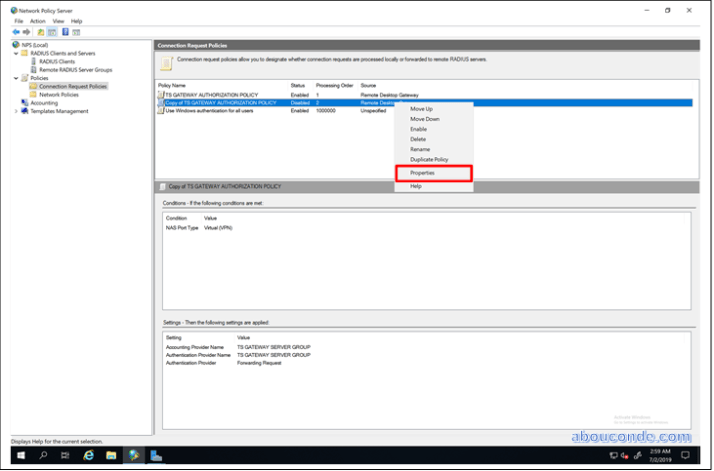
In Policy name, enter a suitable name, such as Azure FMA
TS GATEWAY AUTHORIZATION POLICY. Check Policy enabled.
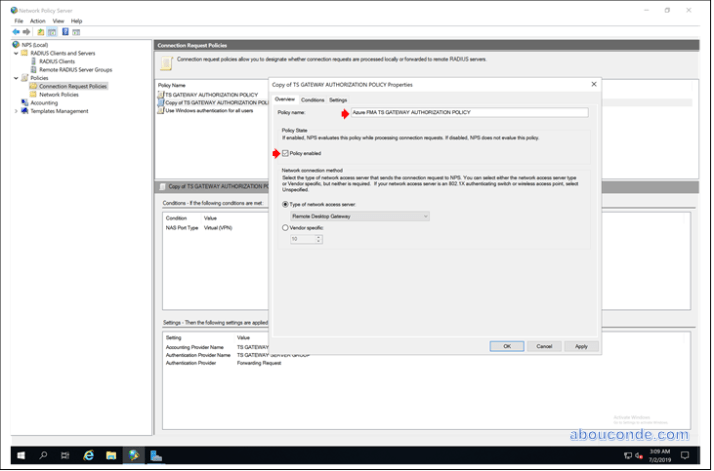
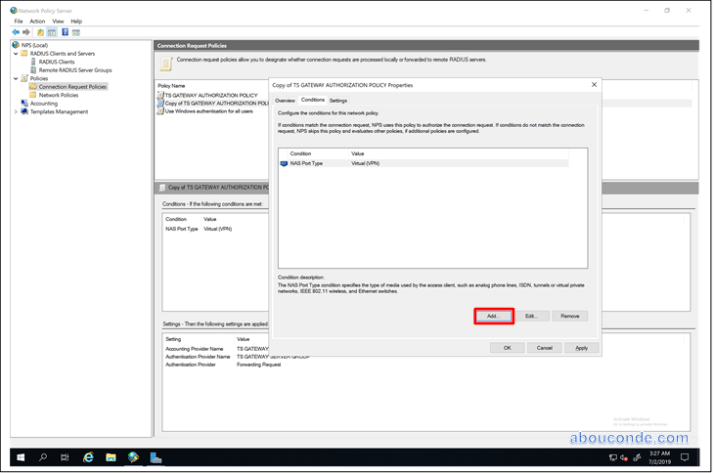
In Conditions tab, click Add
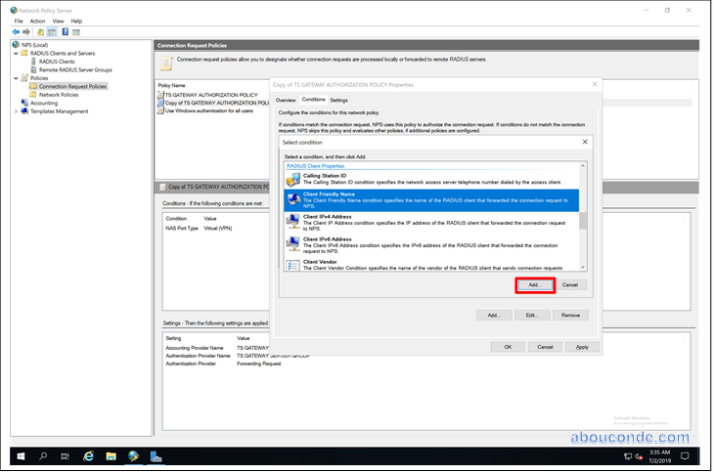
Select Client Friendly Name and Click Add
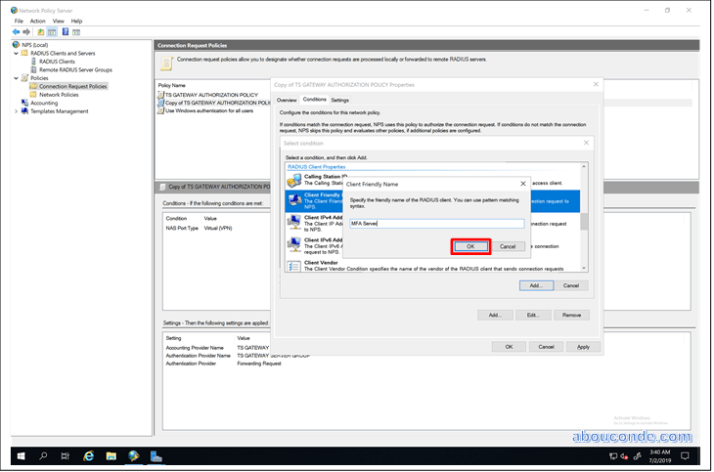
Enter the server friendly name such as MFA Server and click OK
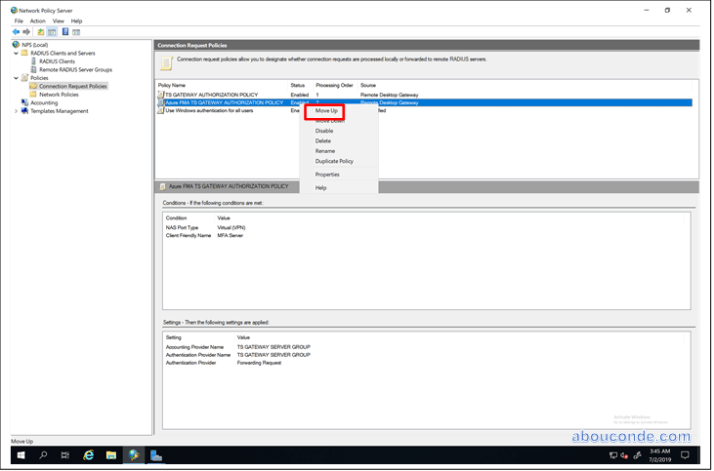
After Creating Connection Request Policy, Right-click and Select Move Up
To prevent a loop condition, make sure that the new policy is ordered ABOVE the original policy in the Connection Request Policies pane.
Go to the Settings tab and select Authentication.
Change the Authentication Provider to Authenticate requests on this server. This policy ensures that when NPS receives a RADIUS request from the Azure MFA Server, the authentication occurs locally instead of sending a RADIUS request back to the Azure Multi-Factor Authentication Server, which would result in a loop condition.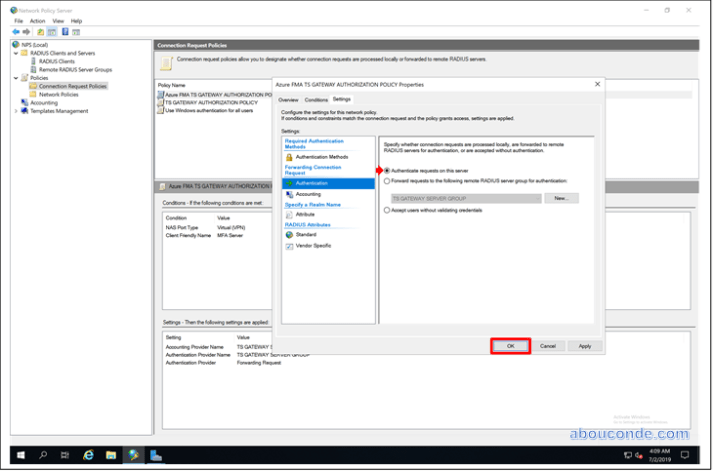
Configure Azure Multi-Factor Authentication
The Azure Multi-Factor Authentication Server is configured as a RADIUS proxy between RD Gateway and NPS. It should be installed on a domain-joined server that is separate from the RD Gateway server. Use the following procedure to configure the Azure Multi-Factor Authentication Server.
Open the Azure Multi-Factor Authentication Server and select the RADIUS Authentication icon.
Check the Enable RADIUS authentication checkbox.
On the Clients tab, ensure the ports match what is configured in NPS then select Add.
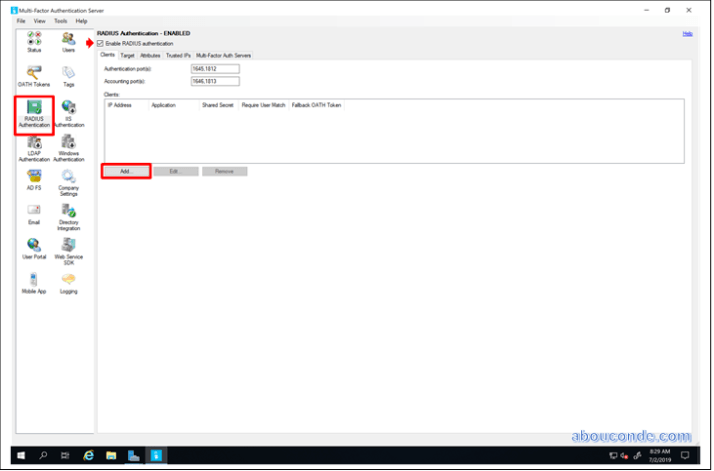
Add the RD Gateway server IP address, application name (optional), and a shared secret. The shared secret needs to be the same on both the Azure Multi-Factor Authentication Server and RD Gateway.

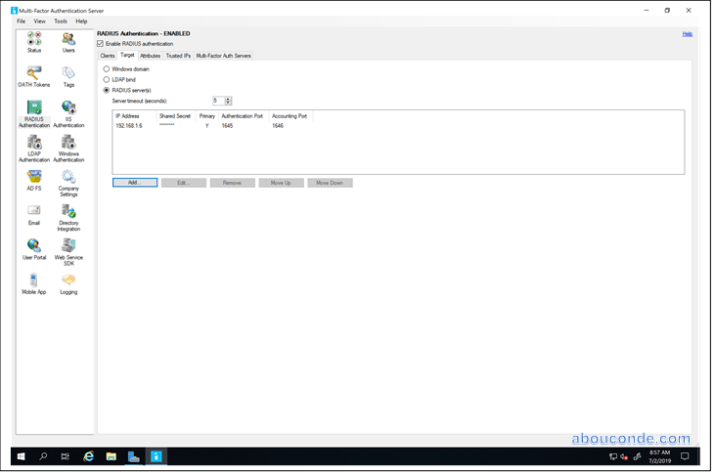
Go to the Target tab and select the RADIUS server(s) radio button.
Select Add and enter the IP address, shared secret, and ports of the NPS server. Unless using a central NPS, the RADIUS client and RADIUS target are the same. The shared secret must match the one setup in the RADIUS client section of the NPS server.

Done

Hi nice blog,do you know if there is a way to link the RDS and NPS to another 3rd party MFA service via radius instead of using Azure MFA?
LikeLike