This blog post shows how to configure company settings, Email Notifications, importing and Managing Users for MFA and Installing the web Services SDK.
The previous post shows how to Implementing Azure Multi-Factor Authentication (MFA) Server On-premises with High Availability (HA)
Configuring Company Settings
You need to configure the MFA server with the default settings it applies to each user account when it is imported or synchronized from Active Directory.
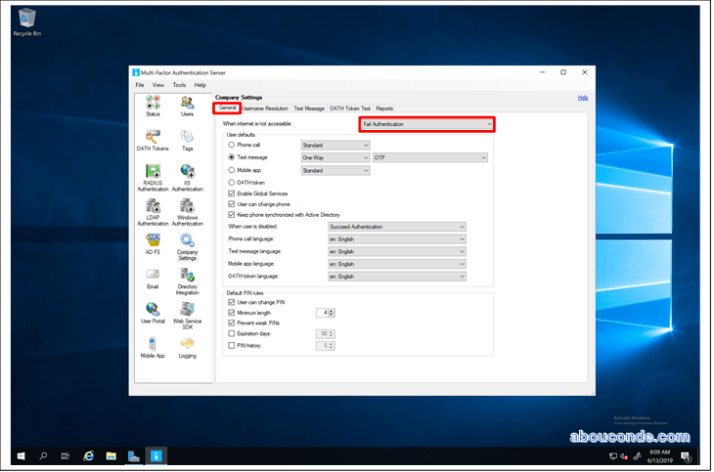
Start the Multi-Factor Server application

Click Company Settings.

On the General Tab, select Fail Authentication from the When internet is not accessible list.
Send users an email
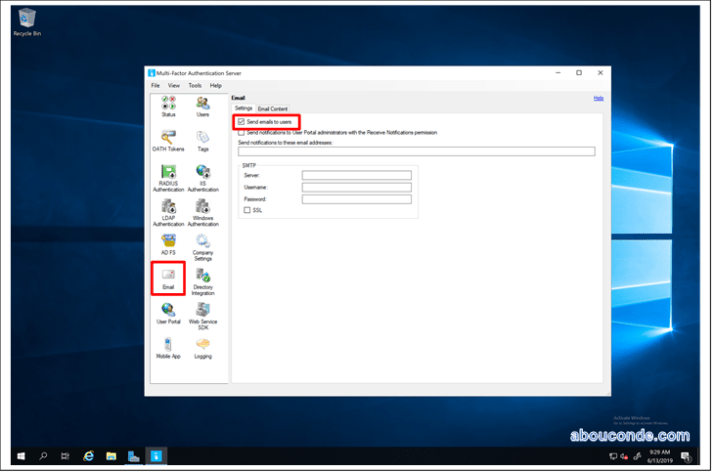
To ease rollout, allow MFA Server to communicate with your users. MFA Server can send an email to inform them that they have been enrolled for two-step verification.
Configure email and email templates
Click the email icon on the left to set up the settings for sending these emails. This page is where you can enter the SMTP information of your mail server and send email by checking the Send emails to users check box.
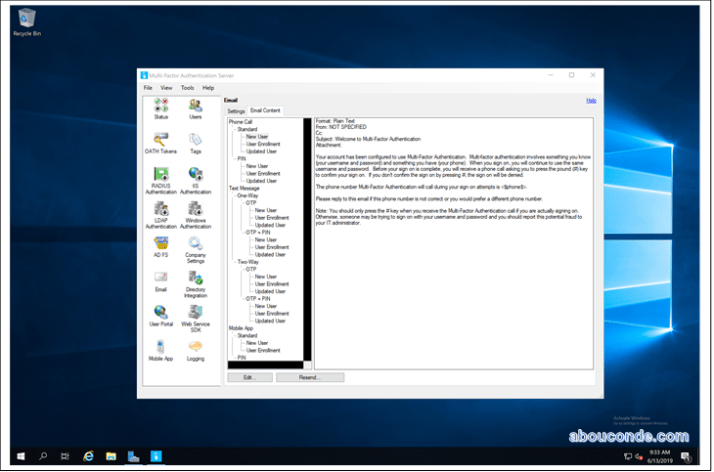
On the Email Content tab, you can see the email templates that are available to choose from. Depending on how you have configured your users to perform two-step verification, choose the template that best suits you.
Import users from Active Directory
Now that the server is installed you want to add users. You can choose to create them manually, import users from Active Directory, or configure automated synchronization with Active Directory.
Manual import from Active Directory
In the Azure MFA Server, on the left, select Users. At the bottom, select Import from Active Directory.

Now you can either search for individual users or search the AD directory for OUs with users in them. In this case, we specify the users OU.
Highlight all the users on the right and click Import. You should receive a pop-up telling you that you were successful. Close the import window. 
Automated synchronization with Active Directory
In the Azure MFA Server, on the left, select Directory Integration.
Navigate to the Synchronization tab. At the bottom, choose Add

In the Add Synchronization Item box that appears choose the Domain, OU or security group, Settings, Method Defaults, and Language Defaults for this synchronization task and click Add.

Installing the MFA Web Services SDK
The Web Service SDK section allows the administrator to install the Multi-Factor Authentication Web Service SDK. The Web Service SDK is an IIS (Internet Information Server) web service that provides an interface for integrating the full features of the Multi-Factor Authentication Server into most any application. The Web Service SDK uses the Multi-Factor Authentication Server as the data store.
Install the Web Server Role
The Azure MFA server does not require the Web Server role, however, User Portal and the optional Mobile Application server communicate with the MFA server database using the MFA Web Services SDK. The MFA Web Services SDK uses the Web Server role.
To install the Web Server (IIS) role,
- Open Server Manager by clicking the Server Manager icon on the desktop.
-
In the Server Manager window, with the Dashboard and Quick Start selected, click Add roles and features, or click the Manage menu, and then click Add Roles and Features. The Add Roles and Features Wizard will start with a Before You Begin page. The wizard asks for verification of the following:
- The administrator account has a strong password.
- The network settings, such as IP addresses, are configured.
- The most current security updates from Windows Update are installed.
- The administrator account has a strong password.
- On the Before You Begin page, click Next.
-
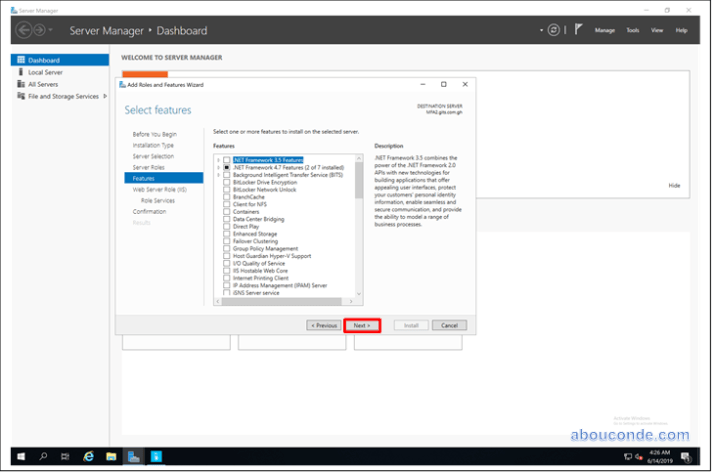
On the Installation Type page, select Role-based or feature-based installation to configure a single server. Click Next.
- On the Server Roles page, select Web Server (IIS).
- In the Add Roles and Features wizard, click Add Features if you want to install the IIS Management Console. If you do not want to install the Management Console, uncheck Include management tools (if applicable), and then click Next.
- On the Server Roles page, select Web Server (IIS).

On the Features page, click Next. Note that you do not need to select any features on this page to install IIS.
IIS setup will select the features that are required.
On the Role Services page, select the following services:
- Common Parameters > Default Document.
- Common Parameters > Directory Browsing.
- Common Parameters > HTTP Errors.
- Common Parameters > Static Content.
- Health and Diagnostics > HTTP Logging.
- Performance > Static Content Compression.
- Security > Request Filtering.
- Security > Basic Authentication.
- Management Tools > IIS Management Console.
- Management Tools > IIS 6 Management Compatibility.
- Application Development > ASP.NET 4.5.
After you have added the role services that you need on the Role Services page, click Next.

On the Confirmation page, verify the role services and features that are selected. Select Restart the destination server automatically if required to restart the destination server if the settings need to take immediate effect. To save the configuration information to an XML-based file that you can use for unattended installations with Windows PowerShell, select Export configuration settings, move to the appropriate path in the Save As dialog box, enter a file name, and then click Save.
When you are ready to start the installation process on the Confirmation page, click Install.

In the left pane of the Multi-Factor Authentication management console, select Web Service SDK.
Click the Install Web Service SDK… button. Click Next here

Accept the default location and click Next.

Click Close

Configure the IIS Server’s Certificate
Installing-and-configuring-certification-authority-on-server-2019
The TLS protocol protects all the communication to and from the MFA server. To enable this protection, you must configure the default web site to use the previously enrolled server authentication certificate.
Start the Internet Information Services (IIS) Manager console
In the navigation pane, expand the node with the same name as the local computer. Expand Settings and select Default Web Site.
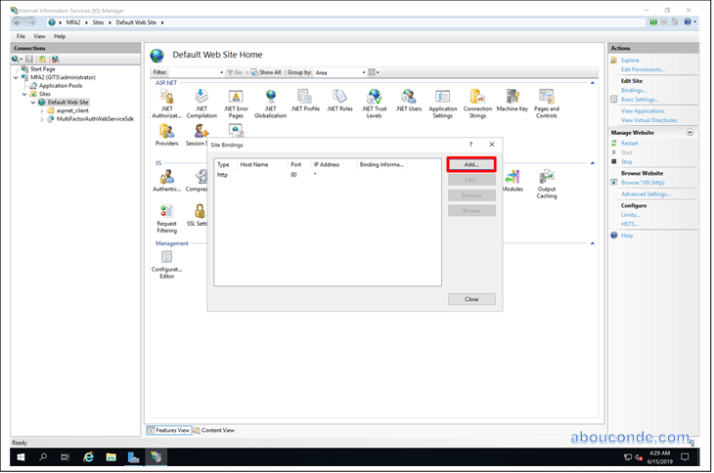
In the Actions pane, click Bindings.

In the Site Bindings dialog, Click Add.
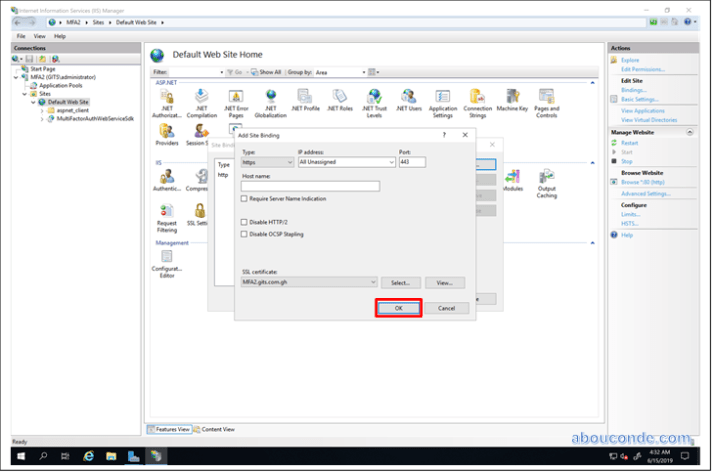
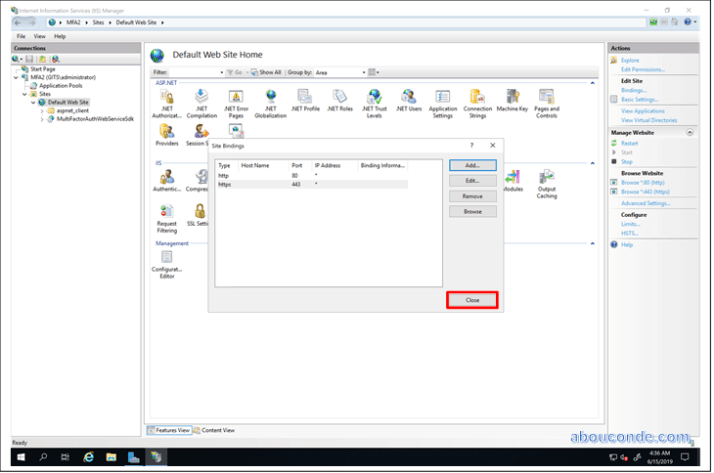
In the Add Site Binding dialog, select https from the Type list. In the SSL certificate list, select the certificate with the name that matches the FQDN of the computer. Click OK. Click Close. From the Action pane, click Restart.
Click Close

One thought on “Getting started with the Azure Multi-Factor Authentication Server (MFA)”