Azure Policy is a service in Azure that you use to create, assign and, manage policies. These policies enforce different rules and effects over your resources, so those resources stay compliant with your corporate standards and service level agreements. Azure Policy meets this need by evaluating your resources for non-compliance with assigned policies.
For example, you can have a policy to allow only a certain SKU size of virtual machines in your environment. Once this policy is implemented, new and existing resources are evaluated for compliance. With the right type of policy, existing resources can be brought into compliance.
This blog post shows how to Defines the resource types that you can deploy in a particular Resource Group.
Create a policy assignment
The process of creating and implementing a policy in Azure Policy begins with creating a policy definition. Every policy definition has conditions under which it’s enforced. And, it has a defined effect that takes place if the conditions are met.
In Azure Policy, there are several built-in policies that are available by default.
- Require SQL Server 12.0: Validates that all SQL servers use version 12.0. Its effect is to deny all servers that don’t meet these criteria.
- Allowed Storage Account SKUs: Determines if a storage account being deployed is within a set of SKU sizes. Its effect is to deny all storage accounts that don’t adhere to the set of defined SKU sizes.
- Allowed Resource Type: Defines the resource types that you can deploy. Its effect is to deny all resources that aren’t part of this defined list.
- Allowed Locations: Restricts the available locations for new resources. Its effect is used to enforce your geo-compliance requirements.
- Allowed Virtual Machine SKUs: Specifies a set of virtual machine SKUs that you can deploy.
- Apply tag and its default value: Applies a required tag and its default value if it’s not specified by the deploy request.
- Enforce tag and its value: Enforces a required tag and its value to a resource.
- Not allowed resource types: Prevents a list of resource types from being deployed.
Allowed Resource Type
Sign in to the Azure portal at https://portal.azure.com with your Azure account.
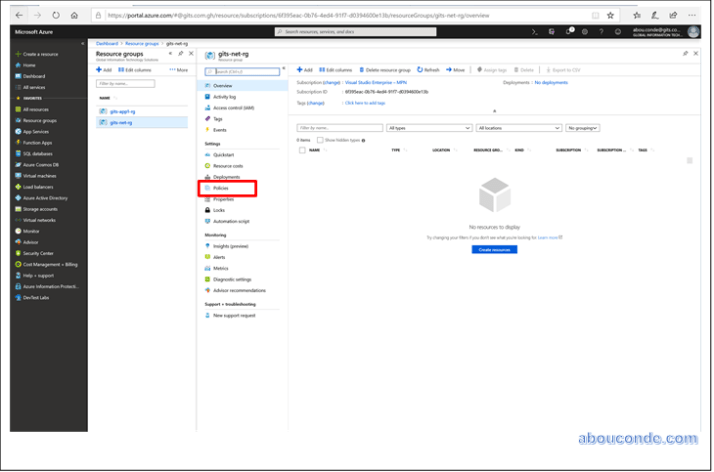
On the left pane of the dashboard, click Resource Groups

Double-Click on the Network resource group

In the Settings blade for the resource group, select Policies.
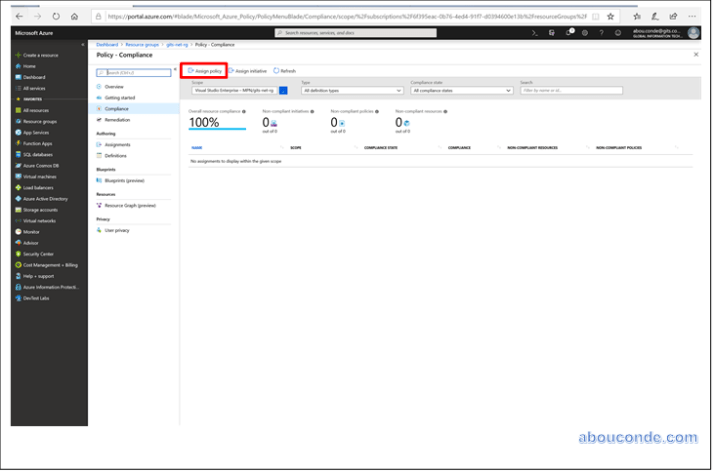
Select Assign Policy from the top of the Policy – Assignments page.
On the Assign Policy page, select the Scope by clicking the ellipsis and select subscription and resource group.
A scope determines what resources or grouping of resources the policy assignment gets enforced on. Then click Select at the bottom of the Scope page.
Resources can be excluded based on the Scope. Exclusions start at one level lower than the level of the Scope. Exclusions are optional, so leave it blank for now.
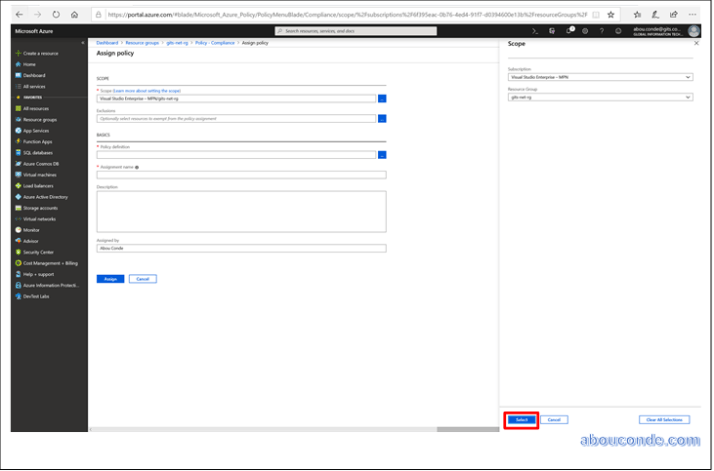
Select the Policy definition
ellipsis to open the list of available definitions. Azure Policy comes with built-in policy definitions you can use.
Search through the policy definitions list to find the Allowed Resource Type definition. Click on that policy and click Select.

The Assignment name is automatically populated with the policy name you selected, but you can change it. You can also add an optional Description. The description provides details about this policy assignment. Assigned by will automatically fill based on who is logged in. This field is optional, so custom values can be entered.

Allowed Resource Type Policy Successfully created

